Research in Network Intrusion Detection
Amazon My professor's lab has developed a network intrusion detection program called LibAnomaly that tries to detect anomalous behavior in a log file or other system-generated records. Basically we want to know if users are not trying to break into the system by issuing dangerous or suspicious system calls.For example, if I observe that this user never touches /sbin/directory for the past 5 years and today he or she accesses the directory, I know something fishy may be going on.
Their system implements several learning models, and I added another model to it. I used a trie, also known as a radix tree, to store training data.
Given the log record, I get a score of each query string in that log depending on how well its prefix is matched, how well its suffix is matched, how many characters are matched, and other measures. The higher the score, the less probability the string is an anomaly.
This is basically a data structure thing; it doesn't really have
anything to do with networking protocol or structure.
Implementing a trie is not simple but doable!
Enjoy the following random pages..
 This website is for Tailwind, a seafood biotech company.
This website is for Tailwind, a seafood biotech company.
 This website is for San Francisco Taiwanese American Festival held annually.
This website is for San Francisco Taiwanese American Festival held annually.
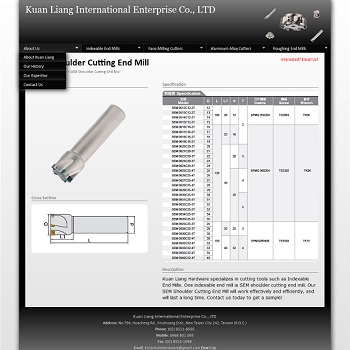 This website is for a Taiwanese company who produces quality end mills and cutters.
This website is for a Taiwanese company who produces quality end mills and cutters.
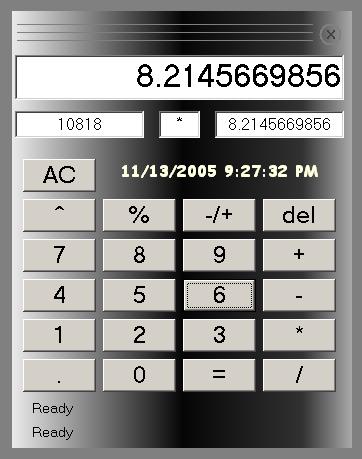 This is a voice-driven calculator program written in VB.
This is a voice-driven calculator program written in VB.

